GCP
Connecting NeuBird to your Google Cloud Platform (GCP) environment enables collection of telemetry data such as resource configurations, audit logs, and metrics. The scope of data accessible depends on the permissions granted to the service account used for the connection.
Step 1: Create a Service Account in GCP
Section titled “Step 1: Create a Service Account in GCP”Create a service account that NeuBird will use to access your GCP resources.
-
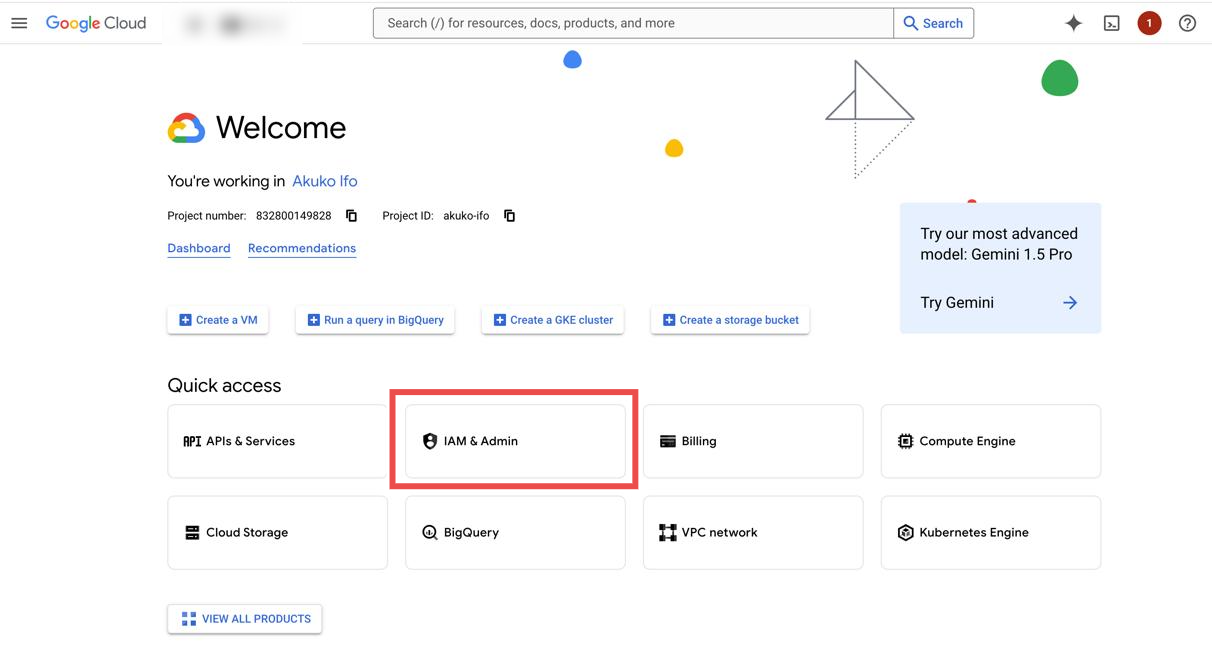
Access IAM & Admin: Navigate to the IAM & Admin section in the GCP Console.
-
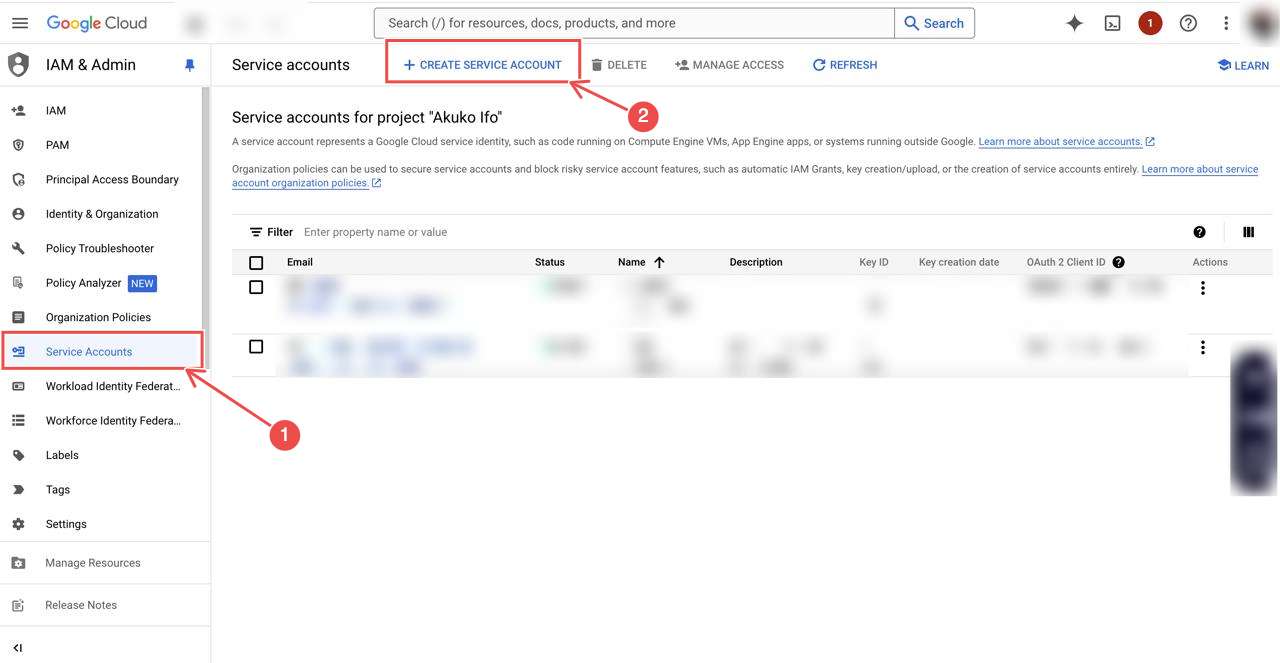
Create a new service account: In the IAM & Admin dashboard, select Service Accounts > Create Service Account.
-
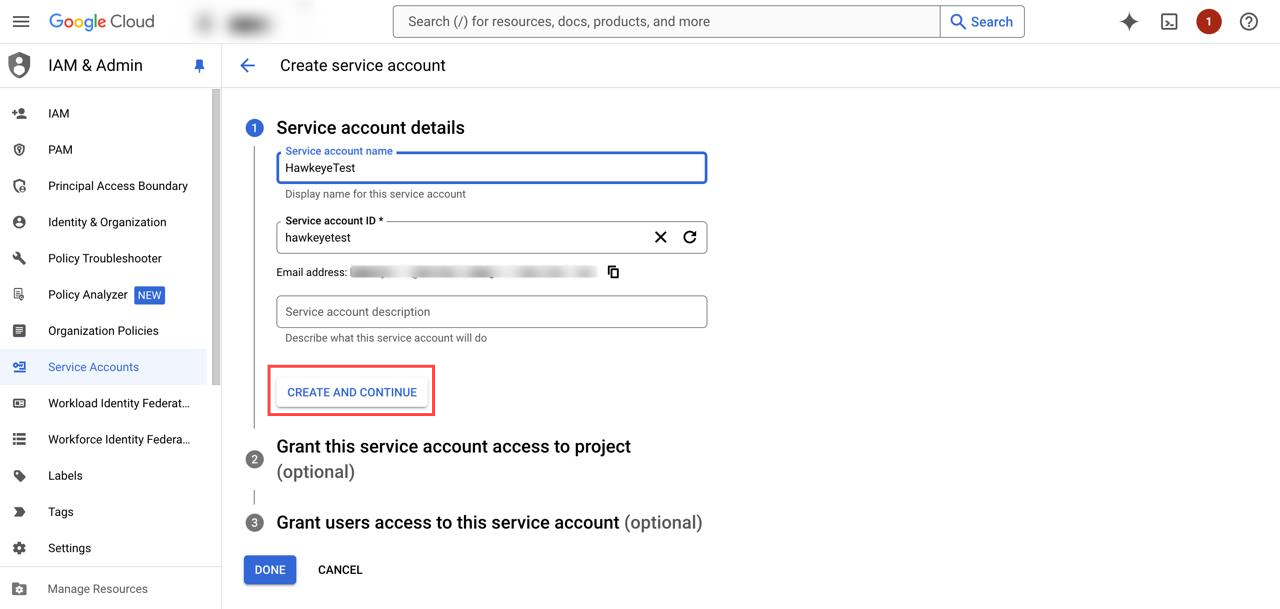
Configure the service account: Enter a Name for the service account and optionally a description. Click Create and Continue.
-
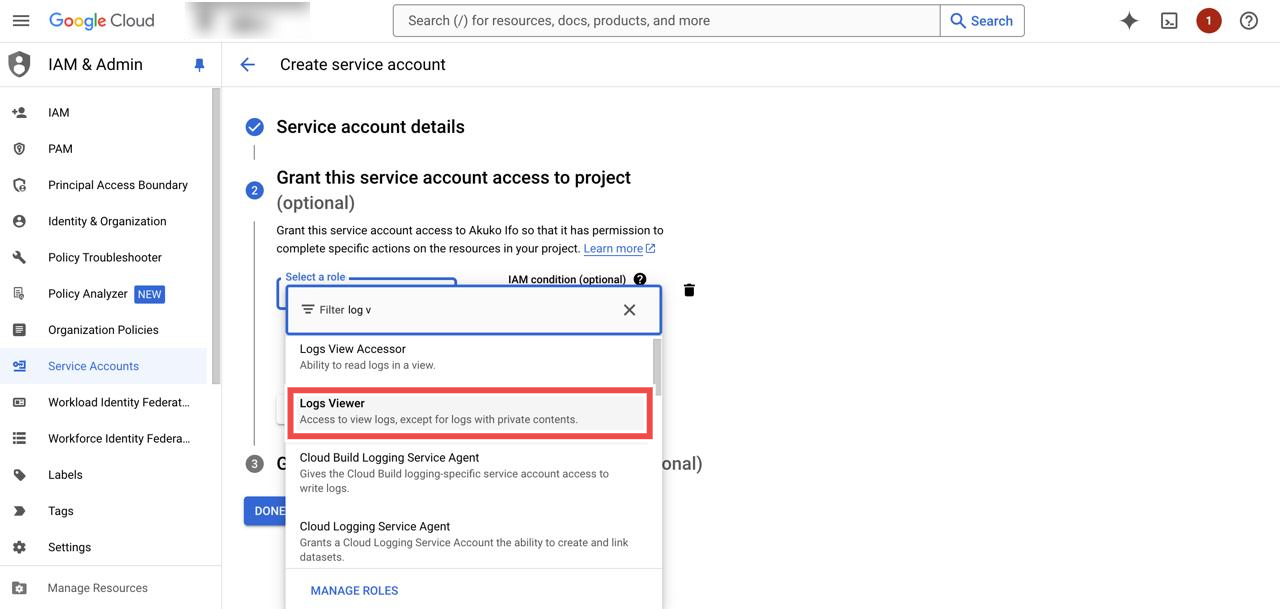
Assign roles to the service account: Assign the following roles:
-
Viewer: Needed for config, logs, and metrics data.
-
Logs Viewer: To access logs.
-
Kubernetes Engine Cluster Viewer: Needed for Kubernetes access to get config for clusters.
-
BigQuery Data Viewer: Needed if you integrate with BigQuery.
Note: NeuBird requires BigQuery to be enabled to ensure accurate analysis.
-
-
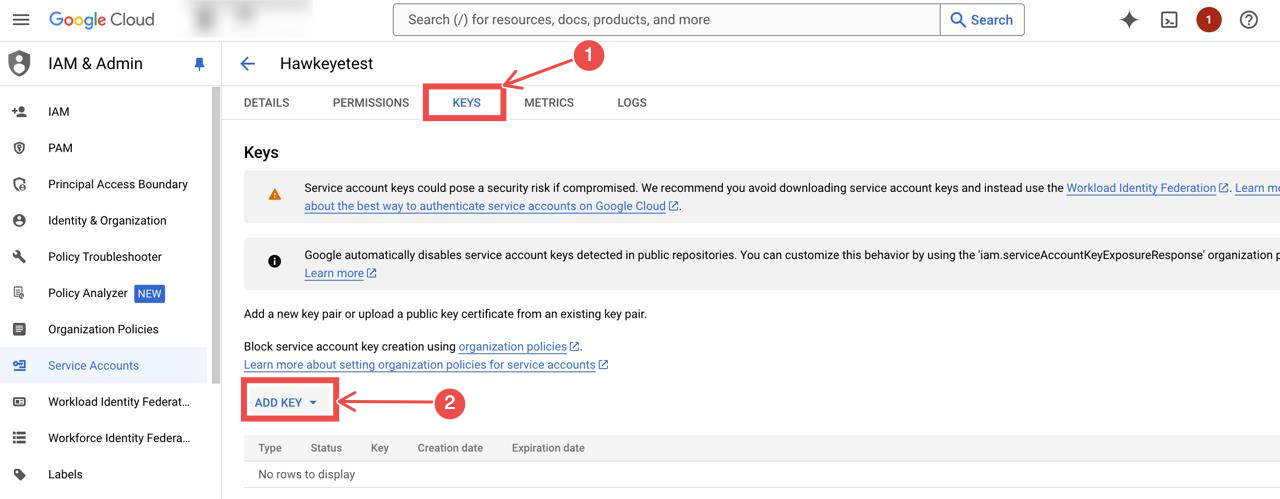
Create a key for the service account: After assigning roles, create a new key for the service account in JSON format. This key will be downloaded to your machine and used to authenticate the connection.
-
Store the service account key: Safeguard this key, as it will be required when configuring the connection.
Step 2: Configure Workload Identity Federation
Section titled “Step 2: Configure Workload Identity Federation”Workload Identity Federation allows external identities to access GCP resources without needing a service account key. It is equivalent to AWS’s external ID for cross-account roles.
-
Create an Identity Pool: In the GCP console, navigate to IAM & Admin > Workload Identity Federation, and create an Identity Pool.
-
Configure an Identity Provider: Add an identity provider to establish trust between the external environment and GCP.
-
Link to Service Account: Attach the Workload Identity Federation to the service account you created, allowing external entities to authenticate and access GCP resources.
Connection Fields
Section titled “Connection Fields”| Field | Required | Description |
|---|---|---|
| Name | Yes | A descriptive name for the connection |
| Description | No | A brief description of the connection |
| Service Account Key | Yes | The JSON key file generated for the service account in Step 1 |
| Project ID | Yes | The GCP project ID where the service account resides |
| Region | Yes | The GCP region where your resources are located |
For general instructions on creating and managing connections, see the Connections Overview.