Console
Overview
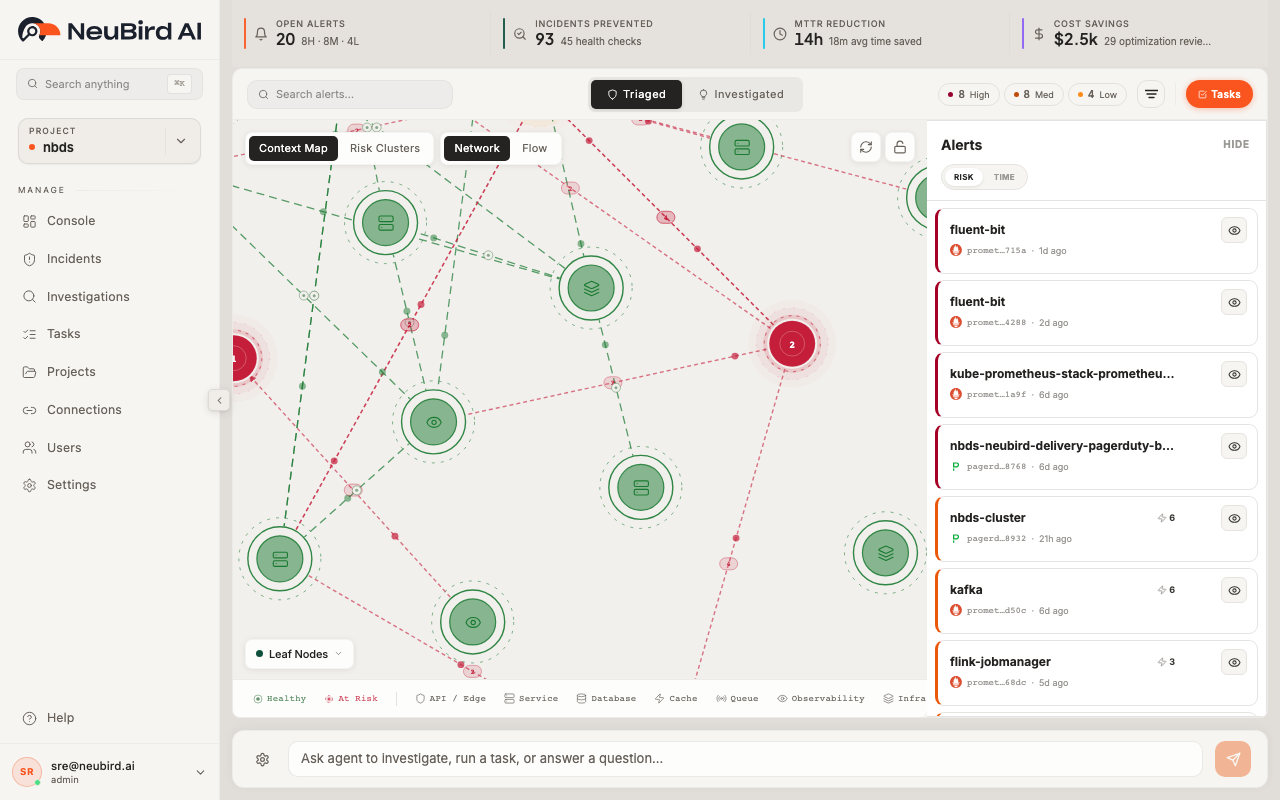
Section titled “Overview”The Console is your main operations dashboard. It gives you a real-time view of system health, active alerts, investigation history, and a service dependency map — all in one screen. Use it to monitor your environment, triage incidents, and launch investigations.
Dashboard Metrics
Section titled “Dashboard Metrics”At the top of the Console, four metric cards summarize your current operational state:
- Open Alerts — the number of unresolved alerts, broken down by severity (High, Medium, Low)
- Investigations — total investigations run, with the number of alerts investigated
- MTTR Reduction — estimated time saved by automated investigations, showing total hours saved
- Agent Confidence — the agent’s average confidence score across all investigations
These metrics update automatically as new alerts arrive and investigations complete. Use them to quickly assess whether your environment needs attention.
Service Map
Section titled “Service Map”The center of the Console shows a service dependency map, which visualizes the relationships between your monitored resources.
You can interact with the map in several ways:
- Context Graph / Risk Clusters — toggle between a dependency view and a risk-based clustering view
- Reset — reset the map zoom and position to the default view
- Unlock — unlock node positions so you can drag and rearrange them
- Fullscreen — expand the map to fill the entire screen (click the expand icon in the bottom right). Press the same button again to exit fullscreen.
When your project has monitored resources configured via Connections, the map populates with nodes representing services, databases, APIs, and infrastructure components. Edges show upstream and downstream dependencies.
Incident Triage
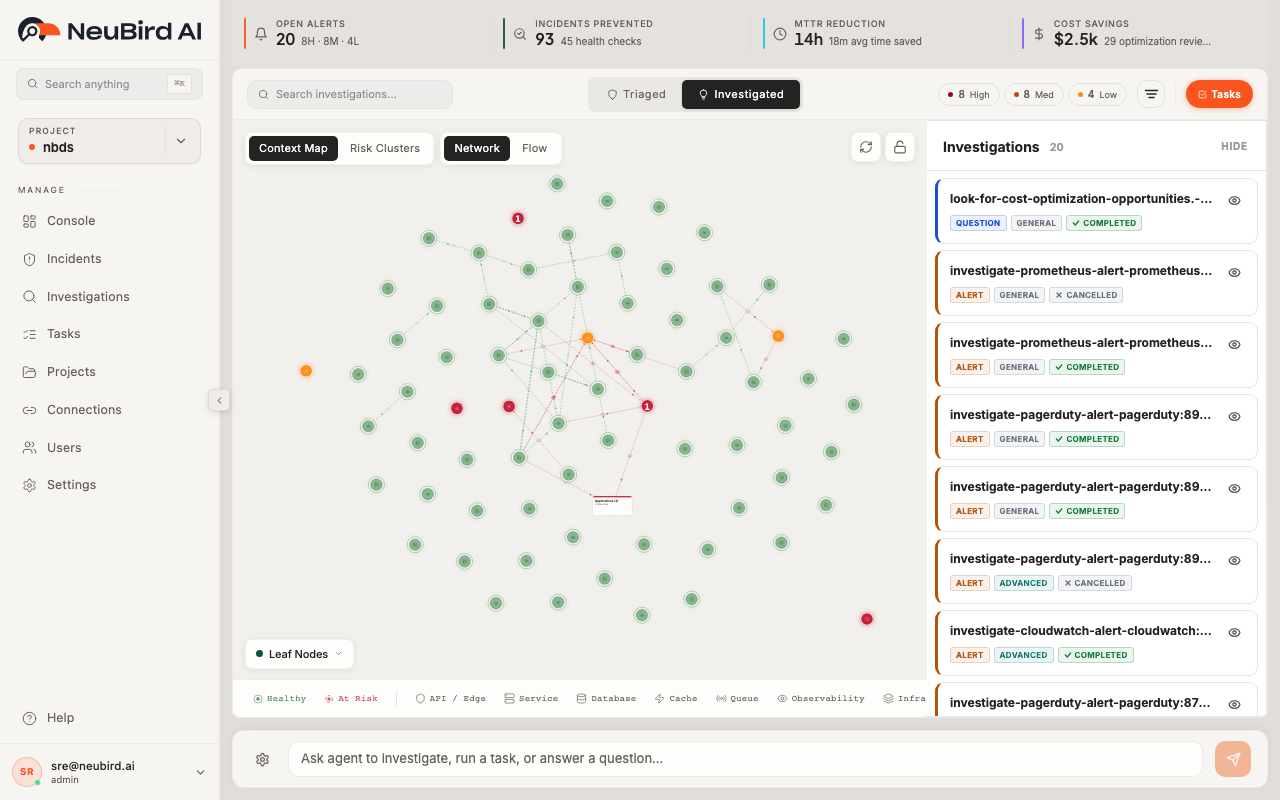
Section titled “Incident Triage”The right side of the Console shows your incidents and investigations. You can switch between two views:
- Triaged — alerts that have been clustered and prioritized by impact risk
- Investigated — a chronological list of all investigations, showing their status, type, and results
In the Investigated view, each investigation card shows:
- Type badge (Question, Alert, Task) — how the investigation was triggered
- Title — a summary of what was investigated
- Investigation ID — a unique identifier for reference
- Mode and Status badges — for completed investigations, shows Advanced/Basic mode and Done status
- Duration and rounds — how long the investigation took and how many reasoning rounds were used
Click any investigation card to open its full report with root cause analysis, findings, and recommendations.
Impact Risk Bar
Section titled “Impact Risk Bar”Above the investigation list, the Impact Risk bar shows a breakdown of open vs. resolved alerts by severity. The colored segments (red for High, orange for Medium, yellow for Low) give you an at-a-glance view of your alert distribution.
Searching
Section titled “Searching”Use the Search field to filter investigations by title or content. Click the filter icon to access advanced filtering options.
Asking the Agent
Section titled “Asking the Agent”Click the Ask Agent button (orange, top left of the content area) to open the agent prompt. Type a question in natural language — for example:
- “Why is the message-processor service failing?”
- “Check system health across all services”
- “Investigate the recent spike in API latency”
The agent starts an investigation immediately and you’ll be taken to the investigation detail page to watch the results as they stream in.
Tasks (Quick Access)
Section titled “Tasks (Quick Access)”Click the Tasks button (next to Ask Agent) to open the quick tasks panel. This shows your configured scheduled tasks with a Run button for each one. You can trigger any task on demand without leaving the Console.
For full task management — creating, editing, scheduling, and viewing run history — use the dedicated Tasks page from the sidebar navigation.